By now, the concept of “DevSecOps” is familiar to just about everyone working in modern software development, with its promise to fundamentally strengthen application security as well as alleviate friction between DevOps and security teams.
Under a DevSecOps model, security is shifted left and baked directly into the DevOps development and deployment process. In particular, security is embedded at every phase of the continuous integration/continuous deployment (CI/CD) pipeline to help identify security flaws earlier. Unlike traditional security models, DevSecOps places security at the heart of development, helping to identify issues closer to their point of origin, to reduce costly (and time-consuming) revisions and prevent vulnerabilities from reaching production.
But despite the push towards DevSecOps, security teams still appear to be lagging behind the pace of DevOps. According to snyk’s DevSecOps Insights 2020 report, 48% of developers still feel security is a major constraint on their ability to deliver software quickly.
Why Is Application Security Still Too Slow?
While most enterprises recognize where their security posture needs to be, intent and reality are two very different things. According to Contrast Security’s The State of DevSecOps Report for 2020, more than 99% of organizations are forced to admit that their average application in production has at least 4 vulnerabilities, while almost 80% report more than 20 vulnerabilities in applications under development. So, even though 70% of security teams surveyed in GitLab’s 2021 Global DevSecOps Survey say they have shifted security left and are collaborating with developers more closely than ever, it’s clear that significant security gaps remain.
Through conversations with NGINX customers, we’ve discovered three broad challenges that continue to slow or block the adoption of DevOps practices by security teams:
- A constantly changing, distributed perimeter
Unlike 20 years ago, security teams are rarely tasked with defending just a single, easy-to-secure perimeter. Instead they must secure apps developed and deployed by DevOps teams that have free rein to choose the environments, platforms, and tools that help them iterate most quickly. DevOps practices are great for innovation, but bad news for the security professionals who must protect a range of services, endpoints, and devices communicating with each other via APIs. In fact, only half of the respondents to the GitLab survey say they have processes for monitoring and protecting apps created using modern development strategies, including microservices and containers. - Inability to automate and embed security policy into CI/CD pipelines
Transformation across different teams is not happening at the same speed, and most of the legacy tools available to security teams weren’t designed for a shifted‑left environment. As a result, security teams are forced to adapt and integrate tools into the pipeline that are poorly suited to automation and modern infrastructures. Even worse, these tools lack self‑service capabilities, so developers and DevOps engineers have to wait to move forward until security finishes a manual audit of policies and processes. - Difficult gaining centralized visibility and security insights
The majority of enterprise apps are not only distributed but also have distributed areas of ownership, each of which uses different tools. This makes it incredibly painful to get consolidated visibility into the security posture within the organization. Instead of digging into the root cause of issues, security teams often waste time trying to consolidate and correlate data from different places.
And of course most enterprises aren’t overcoming these obstacles for just a handful of apps – they are juggling hundreds of products and services spread out across multiple teams running their own technology stacks, toolchains, and processes, all of which require audits and checks to ensure vulnerabilities don’t leave the door open to attacks.
Enterprise Teams Turning to Platform Ops
So, what can you do to help your application security teams become more agile while also empowering developers to continue moving quickly but safely?
The hard truth is that if you can’t find a way to meet the challenges discussed above, you can’t evolve your practices and processes. Iterating faster may feel like the win everyone needs, but the only way to continue scaling DevOps up to its full potential is to make security as frictionless and adaptable as possible across the entire software development lifecycle.
More and more, we’re seeing organizations adopt an approach that – following Gartner’s lead – we call Platform Ops. The core concept is to deliver DevOps capabilities through a platform that’s built to fit the requirements of internal teams within the company. Using internal platforms not only reduces the likelihood of wasting time on redundant tasks, it also helps multiple product teams collaborate continuously and effectively without getting slowed down.
Under a Platform Ops model, security teams provide self‑service, consumable policies to development teams. In addition, security tools are fully integrated into the application delivery process. In this way, developers can deploy faster while still following the best practices, governance, and access requirements set by knowledgeable security experts.
The big win for application security teams is that Platform Ops creates an environment where developers no longer experience security as a hindrance that slows them down, but rather as an integrated part of the processes and tools they already use. This motivates app delivery teams to adopt patterns that ensure better security for the enterprise as a whole.
How NGINX Helps
At NGINX, we recognize the importance of providing tools, such as a web application firewall (WAF), that can easily shift left to deliver security anywhere in development processes and fully integrate with CI/CD pipelines. It’s also critical to have lightweight solutions that won’t hog CPU or slow down performance.
We have also seen that development and DevOps teams are much happier when security is a guardrail rather than a gate. When security provides strong, consistent controls and policies on a shared, self‑service platform, it becomes easier for development and security teams to align on guidelines with minimal interaction and interruption.
Here’s how the NGINX Application Platform delivers just that:
-
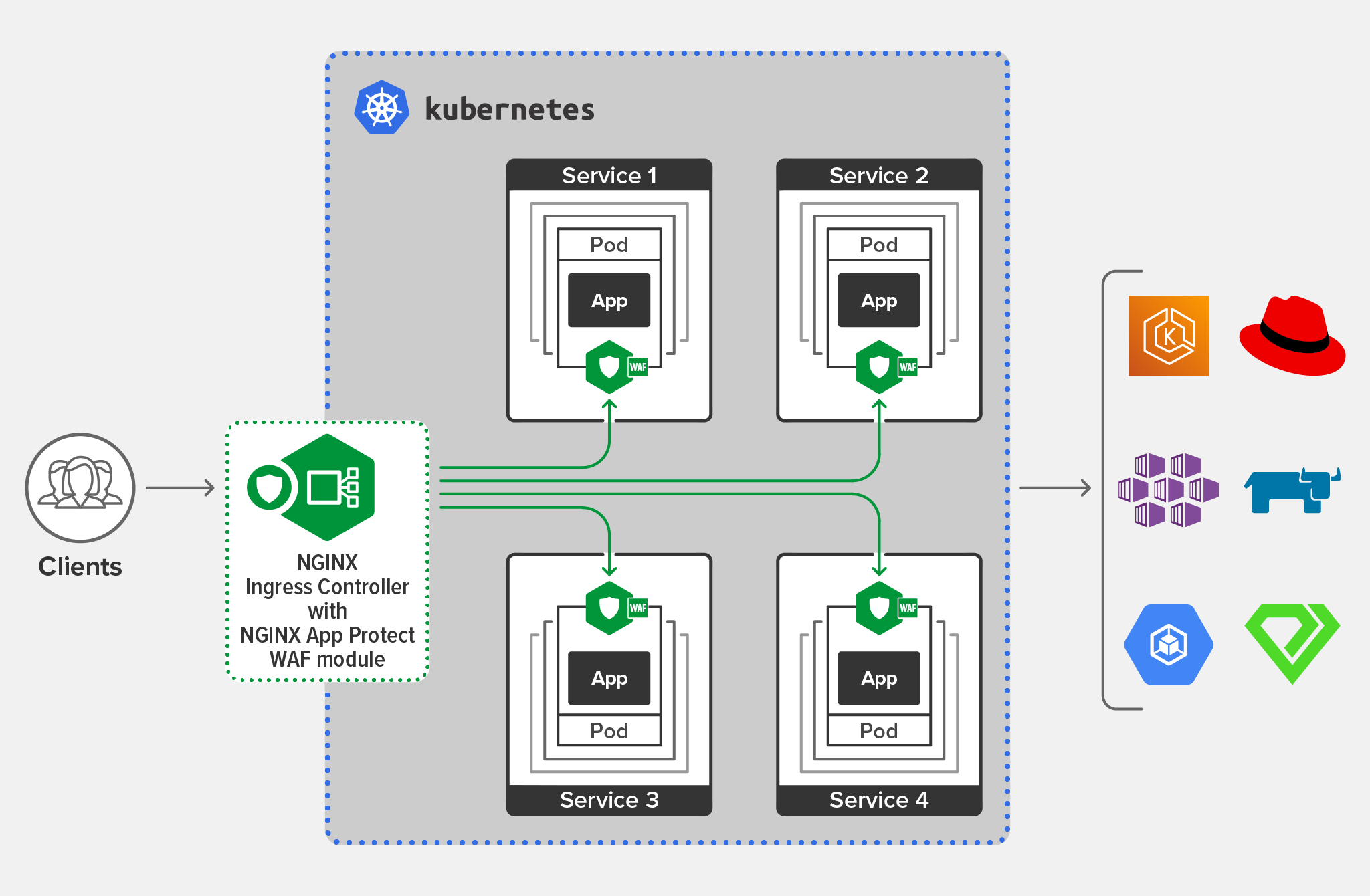
NGINX App Protect WAF is a lightweight, modern WAF you can deploy anywhere you are building and managing apps. Built on F5’s market‑leading WAF technology, App Protect WAF protects against the OWASP Top 10 and other advanced threats regardless of architecture or deployment environment – whether cloud, hybrid, microservices‑based containerized, or on‑premises. Deployed as a dynamic module for NGINX Plus, App Protect WAF enables you to automate security configuration and policies so they can be provisioned directly within your CI/CD pipeline.
-
NGINX App Protect DoS provides automated, adaptive protection to identify and prevent denial-of-service (DoS) attacks. Backed by F5 security experts, App Protect DoS uses adaptive machine learning and built‑in anomaly detection to protect your applications and microservices against application layer attacks. Whether you need to stop a targeted attack or simply prevent an inadvertent misconfiguration from disrupting app performance, App Protect DoS offers zero‑touch protection that seamlessly integrates into modern application architectures, development tools, and frameworks.
-
The NGINX Controller App Security add‑on for the Controller Application Delivery Module enables you to power developer productivity without compromising operations and security compliance. Controller App Security provides trusted app protection and centralized app‑layer threat visibility that can be standardized across HTTP‑based apps and APIs running in multi‑cloud environments. It also enables security teams to provide pre‑approved guidelines which developers and DevOps teams consume in a self‑service manner to easily add app protection to their apps.
-
Advanced security for the NGINX Controller API Management Module enables distributed API security for modern applications:
- NGINX App Protect WAF can now be colocated with API gateways providing API traffic management and security for distributed environments. Enabled by NGINX’s decoupled architecture where the data plane (consisting of API gateways and now NGINX App Protect WAF) has no runtime dependency on the control plane, NGINX delivers best-in-class high performance and security for your APIs that are hosted on‑prem, or public, private, or hybrid cloud.
- The NGINX Controller App Security add‑on for the API Management Module seamlessly integrates strong security with NGINX API gateways deployed anywhere – bare‑metal, VMs, containers, and cloud environments. Out of the box, the add‑on protects against OWASP API Security Top 10 vulnerabilities and others like SQL injection and remote command execution (RCE). It validates allowed file types and response status codes and checks for malformed JSON, XML, and cookies. The add‑on also detects evasion techniques used to mask attacks and ensures compliance with HTTP RFCs.
Ready to Make Security Easy and Pain-Free?
Start free 30‑day trials of NGINX Plus with NGINX App Protect and NGINX Controller, check out our offerings in the cloud (AWS, Google Cloud Platform, Microsoft Azure), and enroll in the instructor‑led class Intro to NGINX App Protect.